When social security numbers and other personally identifiable information (PII) are leaked from exploited databases by ransomware groups, it allows cybercriminals a wide range of possible financial identity attacks.
While these groups typically search for attack paths with the least resistance, their primary aim is to hit a victim’s “digital nerve center” - web browsers. That’s because browsers store a large amount of valuable authentication data and don’t generally require a modicum of authentication to access the browser and begin siphoning the data.
Infostealer malware scrapes browsers for the following:
- Saved passwords, since most browsers store login credentials locally
- Session cookies
- Autofill data
- Cryptocurrency wallets
- Clipboard contents
- VPN credentials
- Email account logins
- Browser tokens for sites like Gmail, Discord, Telegram, etc.
Built-in Password Managers
By nature, browsers contain a vast wealth of user data, which is precisely why infostealer malware was created, which takes full advantage of the fact that user credentials are hiding in plain sight. You click your browser’s icon, and it opens, no password required. Very few modern browsers require a password to access their password vault.
What happens if your default browser’s password vault is locked? It doesn’t stop the attack. Infostealer malware then looks for session cookies. These can allow attackers to reuse an active login session without needing the password, whether that be Facebook, banking, email, etc.
Next, the infostealer malware may search for autofill data, such as names, addresses, phone numbers, email accounts, credit card numbers, and even shaded passwords, which can be unshaded to reveal what they are.
Attackers are also looking for FTP/SSH clients with stored credentials in the configuration files. Basically, any nexus point of data that can possibly bridge them with more data to compromise is key. This includes cloud storage like OneDrive, Dropbox, Google Drive, and so on.
Many infostealers also include keylogging modules, so if the attacker’s scope is to harvest more information or capture credentials or 2FA codes they weren’t able to scoop up, capturing keystrokes is the next logical step.
Even if your browser’s password manager is protected, it doesn’t stop the malware from carrying out its objectives.
This rabbit hole goes even deeper.
Email Accounts: Your Digital Junk Drawer
Let’s face it: Email accounts have become everybody’s digital junk drawer. After all, we use them for registering and even authenticating with virtually every service we use, or used to use, but never unsubscribed or removed.
So, now we end up accumulating an overwhelming amount of private information all confined to a single account. Because of this, most people will create one password to rule them all. That way, we don’t end up forgetting. Attackers are expecting users to do this, which makes their objectives that much easier to accomplish.
This isn’t theoretical, it’s the reality every internet user faces in the wild west of the web. If a hacker gains access to your email account, they can reset and take control of virtually every service linked to that address, including your 2FAs.
Reducing Attack Scopes: Using an External Password Vault
Using password managers like LastPass, Bitwarden, 1Password, or many others on the market does significantly reduce the damage from credential theft, but they do not stop attackers from stealing session cookies if the operating system itself is compromised.
Malware usually cannot directly read saved passwords from the browser’s password database. Furthermore, attackers cannot easily dump hundreds of saved credentials in the same way they can from a browser’s built-in password vault.
So, even if encrypted password vaults are stolen, they are encrypted and very difficult and time-consuming to decrypt without the master password. Most ransomware gangs do not want to waste time pursuing something that might be fruitless when that time could be invested in looking for a less secure environment to pilfer.
This means password managers greatly reduce the risk of password theft. Even if cookies are stolen, a proper password manager can still help because attackers cannot dump all your stored passwords, log into accounts that require a fresh authentication, or change passwords on accounts they cannot access via session tokens.
Furthermore, password managers can also automatically fill in your credentials, which reduces the risk of keyloggers capturing your passwords and prevents them from being exposed in the login field.
Even better, if you use a dedicated password manager, you can generate a unique password for each site. That way, if one service suffers a data breach, attackers cannot realistically reuse the stolen password to access your other accounts. You don’t have to remember complicated passwords across multiple sites if you use this method and let your password vault do the heavy lifting.
How Can You Secure Session Cookies?
Session cookies are difficult to protect because they have to exist in a readable form in the web browser while you’re logged in. This means if infostealer malware has access to your system, it can usually copy them. However, there’s good news, because session cookies exist with several security layers that can reduce the risk of session cookie theft.
Websites can configure cookies with security attributes that make them harder to steal. For example, cookies can be restricted to HTTPS connections using the Secure flag. The HttpOnly flag prevents JavaScript from accessing the cookie, which blocks many cross-site scripting (XSS) attacks.
Some services, such as Discord, Telegram, Facebook, LinkedIn, Upwork, and many others, also bind session tokens to characteristics such as device fingerprints, TLS sessions, hardware IDs, or IP addresses. This means that even if someone hijacks a session token that keeps you signed in, the server may block access attempts that do not match the device or environment normally used to log in.
A tried and true solution to not play Russian roulette with your session cookies is simply to manually log out of accounts after use. Logging out tells the server to invalidate the session token, so the cookie can no longer be used.
Hardware-based Multi-Factor Authentication
While password managers store all your passwords in an encrypted vault, hardware-based MFA doesn’t store all passwords. They are designed to protect high-value accounts such as email accounts, VPNs, banking, or corporate apps.
Instead of revealing a password, password managers generate a one-time cryptographic proof that’s connected to the physical device. So, if your password is stolen, an attacker can’t log in without the physical hardware device itself. Ultimately, it's about adding an additional layer of authentication instead of managing credentials.
Be part of the resistance, quietly.
Get Mysterium VPN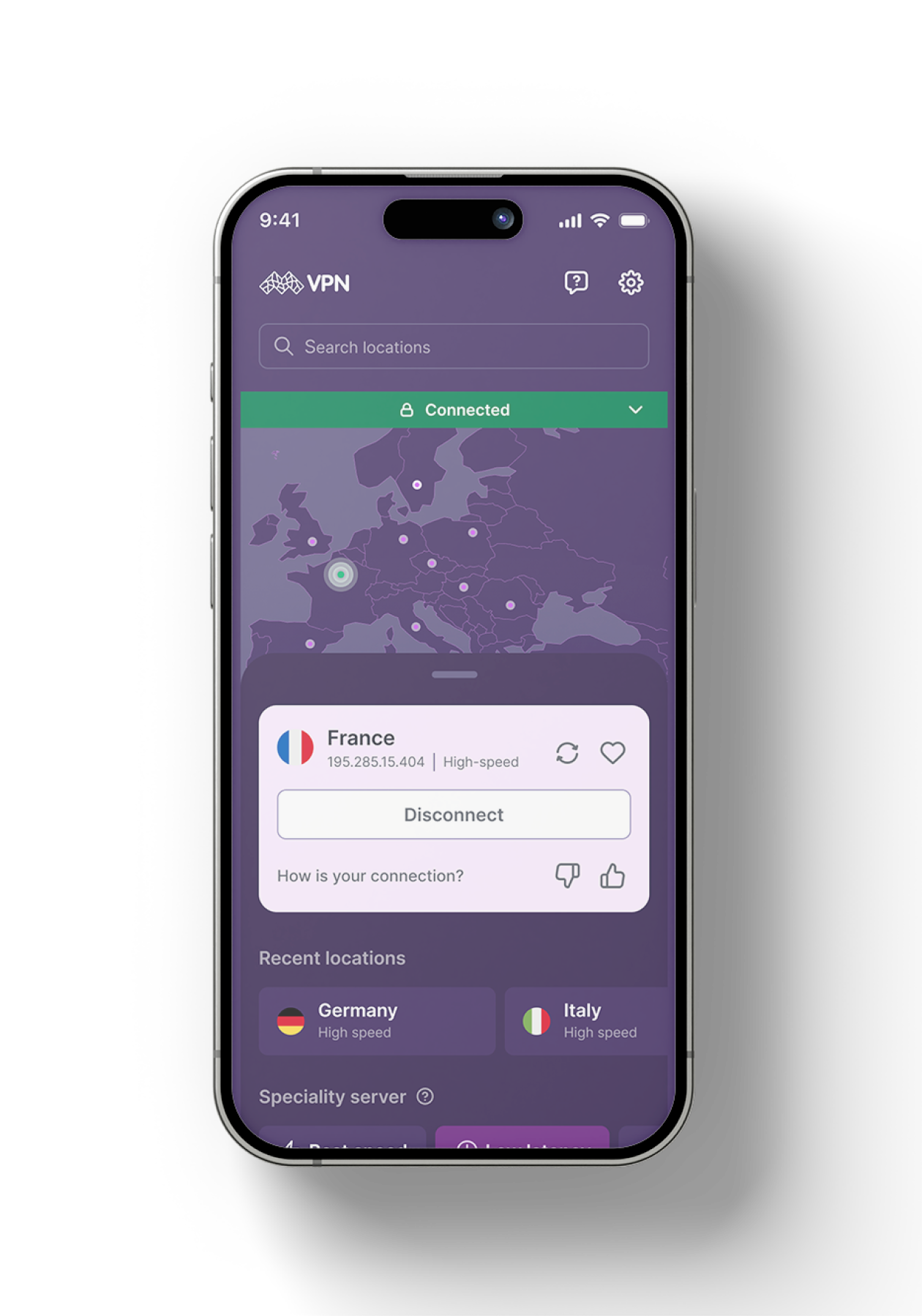

Jesse William McGraw, also known as GhostExodus is a former insider threat and threat actor. He became the first person in recent U.S. history to be convicted of corrupting industrial control systems. Nowadays he focuses on threat intelligence, OSINT, and public speaking, uses his knowledge to bring awareness to security risks.


.png)