What's Really Running Inside Your Free VPN: A Mysterium VPN Research

Free VPN apps are one of the most downloaded and least examined categories of software on Android. The promise is privacy, the price is zero, and most users never look further than the install button. But there’s a good reason why we keep speaking out against using free VPNs time and time again, and this time, we brought concrete evidence to back it up.
The reality with such things is rarely as pretty as it appears on the surface. We ran a static analysis on 18 of the most popular free Android VPN apps available on the Google Play Store, using MobSF (Mobile Security Framework) to examine declared permissions, embedded tracking libraries, hardcoded network endpoints, and connections to OFAC-sanctioned jurisdictions.
What the analysis found is not a surprise if you understand the business model. And yet, it is still absolutely worth documenting in full, because most free VPN apps are nowhere near the privacy tools they pretend to be.
Key Findings
- 17 out of 18 apps contained at least one embedded advertising or analytics tracker.
- The average app included 4.9 trackers, with the worst offender packing 14.
- FreeVPN was the only tracker-free app, yet it requested 12 dangerous permissions, including camera, microphone, contacts, and call logs.
- 6 apps communicated with domains flagged under OFAC sanctions.
- 5 apps connected to servers located in mainland China; 3 apps connected to Russian infrastructure.
- 15 out of 18 apps contained Google AdMob advertising code.
- VPN 360 communicated with 105 unique hardcoded domains, for an app whose sole purpose is to create a secure tunnel.
How We Conducted the Research
We selected 18 free Android VPN applications based on their popularity, download count, and visibility in Google Play Store search results for "free VPN." Each APK was analyzed using MobSF (Mobile Security Framework), an open-source automated mobile application security testing framework that performs static analysis without executing the app, extracting data directly from the application package.
We examined four categories of data:
- Declared permissions: Every Android permission the app requests, categorized as normal, dangerous, or unknown. We flagged permissions commonly associated with spyware and stalkerware.
- Embedded trackers: Third-party tracking libraries detected within the app's code, matched against the Exodus Privacy tracker database of 432 known trackers. These include advertising SDKs, analytics platforms, and behavioral profiling tools.
- Network endpoints: Hardcoded URLs and domains found in the app's code, including API endpoints, ad servers, and analytics services. We geolocated these domains and checked them against OFAC sanctions lists.
- Embedded emails: Developer and third-party email addresses found within the application code.
One important note: static analysis reveals what an app is built to do and what it contains, not necessarily what it does at every runtime session. A declared permission does not always mean active exploitation, and an embedded tracker does not always mean data is being exfiltrated. In a privacy tool, however, the presence of these elements is itself the finding, and an alarming one at that.
Embedded Trackers – The Advertising Machine
Trackers are third-party software libraries bundled into an app that collect user data for advertising, analytics, or behavioral profiling. Finding them inside a VPN app, a tool people use specifically to avoid being tracked, is about as contradictory as it gets.
Scale of the Problem
Out of 18 apps tested, 17 contained at least one embedded third-party tracking library. The single exception was FreeVPN, which, as detailed below, compensates with a different approach entirely. The average app contained 4.9 embedded trackers.
Google's Dominance
Google's own advertising and analytics infrastructure was embedded across nearly the entire dataset:
- Google AdMob (mobile advertising): 14 out of 18 apps (78%)
- Google Firebase Analytics: 15 out of 18 apps (83%)
- Google Crashlytics (crash reporting): 13 out of 18 apps (72%)
While Crashlytics serves a legitimate function, the near-universal presence of AdMob confirms what the business model requires: these apps monetize through advertising, and advertising requires behavioral data collection.
Top Offenders by Tracker Count
| App | Trackers | Notable Trackers |
| Turbo VPN | 14 | Facebook Ads, Flurry, Mobvista, Umeng, Cloudmobi, DuApps |
| VPN 360 | 12 | Facebook Ads, Mintegral, Unity3d Ads, Inmobi, ironSource |
| VPN Proxy Master | 10 | Yandex Ad, Inmobi, Unity3d Ads, ironSource, Adjust |
| Secure VPN | 7 | Facebook Ads/Analytics/Login/Share, Google AdMob |
| Unseen Online | 7 | AppBrain, Facebook Ads/Analytics/Login, Google AdMob |
Disclaimer: Data was captured in March 2026.
Chinese and Russian Ad Platforms
Several apps went beyond Google and Facebook to embed advertising infrastructure from Chinese and Russian platforms:
- Turbo VPN contained Umeng Analytics (owned by Alibaba), Mobvista, Cloudmobi, and DuApps, all Chinese advertising and analytics platforms.
- VPN Proxy Master included Yandex Ad, the Russian advertising platform.
- VPN 360 embedded Mintegral, another Chinese ad platform, alongside multiple ad mediation SDKs.
- Facebook integration in some form (Ads, Analytics, Login, or Share SDK) appeared across 5 apps, enabling cross-platform behavioral profiling.
Users download VPN apps to stop being tracked online. The majority of free VPN apps are themselves packed with the very tracking infrastructure users are trying to escape. That is a fundamental betrayal of the product's core promise.
Dangerous Permissions – What These Apps Can Actually Access
A legitimate VPN application requires exactly three things to function: network access, the ability to create a VPN tunnel, and foreground service rights. Any permission beyond that list has no relationship to VPN functionality.
FreeVPN – Spyware-Grade Permissions
FreeVPN stands out as the most permission-hungry app in the dataset, requesting 21 total permissions, of which 12 are classified as dangerous by Android's permission system. These include:
- CAMERA – can take photos and videos at any time
- RECORD_AUDIO – access to the device microphone
- READ_CONTACTS – access to the user's full address book
- READ_CALL_LOG – access to call history
- ACCESS_FINE_LOCATION + ACCESS_BACKGROUND_LOCATION – precise GPS tracking, even when the app is not in use
- READ_PHONE_STATE + READ_PHONE_NUMBERS – access to device identity and phone number
- READ_EXTERNAL_STORAGE + READ_MEDIA_IMAGES – access to files and photos stored on the device
There is no VPN function that requires access to a user's camera, microphone, address book, or call history. This permission profile is structurally indistinguishable from stalkerware.
Notably, FreeVPN was the only app in the dataset with zero embedded trackers, likely because it has no need for third-party tracking libraries when it can collect data directly through OS-level permissions.
Other Notable Permission Requests
- VPN Proxy Master requested 23 permissions, with 6 dangerous ones, including camera access and background location tracking.
- Secure VPN and VPN 360 each requested 24 total permissions, the highest count in the dataset.
- Quark VPN requested WRITE_SETTINGS and SYSTEM_ALERT_WINDOW, permissions that allow an app to modify system settings and draw overlays over other applications, a technique used in clickjacking attacks.
Dangerous Permission Distribution
Across all 18 apps, the most commonly requested dangerous permissions were:
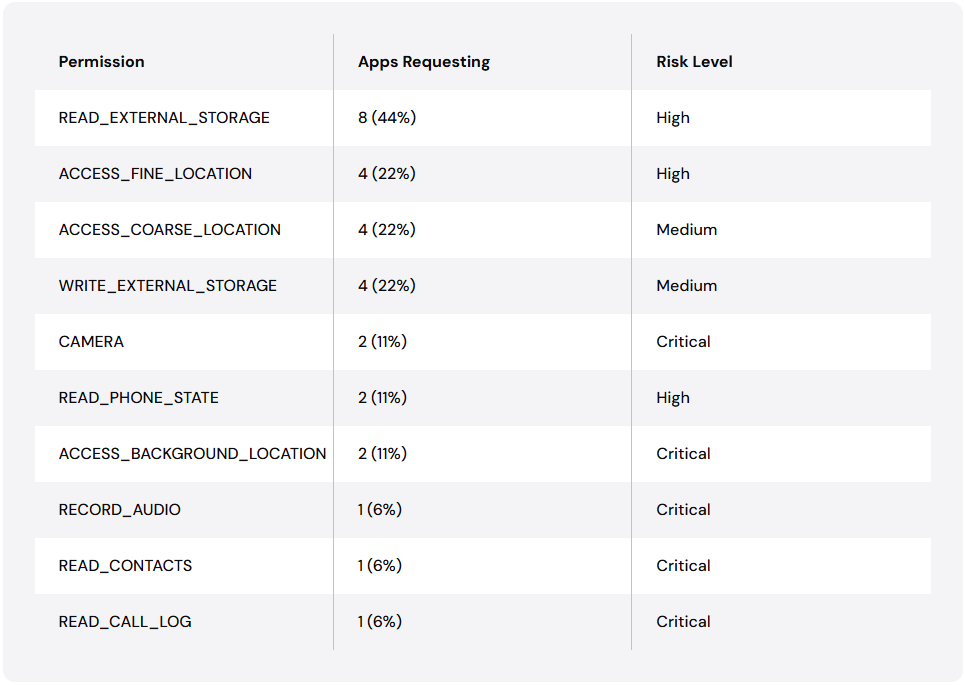
Disclaimer: Data was captured in March 2026.
Connections to Sanctioned Jurisdictions
Beyond trackers and permissions, perhaps the most alarming finding is the number of free VPN apps that contain hardcoded connections to servers in countries subject to OFAC sanctions or with documented state surveillance programs. Routing VPN traffic through these jurisdictions exposes users to risks that no tracker policy or permission review can address.
OFAC-Flagged Domains
Six out of 18 apps (33%) contained domains flagged as potentially OFAC-sanctioned:
| App | Flagged Domains | Country |
| Turbo VPN | cmnsguider.yunos.com, log.umsns.com | China |
| Turbo VPN Lite | baidu.com | China |
| Urban VPN | dns.alidns.com | China (Alibaba DNS) |
| VPN Monster | m.baidu.com, baidu.com | China |
| VPN Proxy Master | cdn.zmaticoo.com + 3 others | China + unknown |
| VPN 360 | baidu.com | China |
Disclaimer: Data was captured in March 2026.
Connections to China
Five apps contained hardcoded domains resolving to servers in mainland China. For a VPN application, routing any traffic through Chinese infrastructure carries specific and serious risks:
- Chinese law requires technology companies operating in China to cooperate with state security services.
- China's mandatory data retention laws mean user data cannot simply pass through Chinese infrastructure without being logged.
- The Great Firewall's deep packet inspection capabilities mean Chinese infrastructure is specifically designed to analyze traffic content, not merely route it.
So, for example, Turbo VPN's code is connected to yunos.com (Alibaba's mobile OS platform) and umsns.com (Umeng social analytics), both geolocating to Chinese servers, alongside 14 embedded trackers, including the Chinese analytics platforms Umeng, Mobvista, and Cloudmobi. That’s quite something to think about.
Connections to Russia
Three apps contained domains resolving to Russian servers:
- VPN Proxy Master connected to 5 Russian domains, including yandex.com, yandex.ru, appmetrica.io, and startup.mobile.yandex.net. It also embedded the Yandex Ad tracker.
- PowerVPN connected to tech.yandex.com and startup.mobile.yandex.net and included AppMetrica, Yandex's analytics platform.
- VPN Monster connected to yandex.com alongside its Chinese Baidu domains.
A VPN app that embeds Chinese analytics libraries and connects to Russian advertising platforms is, at minimum, sharing user metadata with infrastructure in jurisdictions where that data enjoys little to no legal protection. There’s absolutely nothing private or secure about it.
Network Endpoint Analysis
The number of unique domains hardcoded into each app's code provides a direct measure of how many external services the app is built to communicate with. A legitimate VPN client should communicate with a small number of its own servers and perhaps a handful of standard update or crash-reporting endpoints.
Domain Count by App
VPN 360 and VPN Proxy Master each communicated with around 100 unique third-party domains, a staggeringly high number for apps whose stated purpose is to create a single secure tunnel.
| App | Unique Domains | Risk Assessment |
| VPN 360 | 105 | Very High |
| VPN Proxy Master | 99 | Very High |
| Urban VPN | 39 | High |
| VPN Monster | 36 | High |
| VPN free for android | 32 | Medium-High |
| Turbo VPN Lite | 29 | Medium |
| Turbo VPN | 28 | Medium |
| Eco VPN | 26 | Medium |
| Unseen Online | 25 | Medium |
| Secure VPN | 20 | Medium |
Disclaimer: Data was captured in March 2026.
Plaintext HTTP Connections
Several apps contained hardcoded HTTP (not HTTPS) URLs for their own API endpoints or third-party services. Using unencrypted connections in a privacy application is a direct contradiction of the product's stated purpose:
- Turbo VPN contained over 30 plaintext HTTP URLs, many pointing to advertising and analytics endpoints.
- VPN free for android contained over 45 HTTP URLs.
- Ultimate VPN connected via plaintext HTTP to hardcoded server list domains, including premiumvpnlist.com and deindex.biz.
Individual App Risk Profiles
Below are the five apps that presented the most significant combined risk across permissions, trackers, and network connections, followed by a full comparison table of all 18 apps tested.
FreeVPN – Spyware-Grade Permissions, Zero Trackers
FreeVPN's permission set is more consistent with surveillance software than a privacy tool. Its 12 dangerous permissions cover camera, microphone, contacts, call logs, precise and background location, phone state, phone number, and device storage, giving it direct API-level access to virtually everything on the device.
Meanwhile, its source code, which is publicly available on GitHub (cyclelove-bit/freevpn_android), distributes server nodes via a Telegram channel. Both of these things are clear indicators of an individual developer operation rather than a professional security organization.
VPN Proxy Master – Maximum Data Collection
VPN Proxy Master represents the most comprehensive data collection apparatus in the dataset by any combined measure:
- 23 total permissions, 6 dangerous (including camera and background location)
- 10 embedded trackers, including Yandex Ad
- 99 unique hardcoded domains
- 4 OFAC-flagged domains
- Active connections to both Chinese and Russian server infrastructure simultaneously
No other single app combined all of these risk vectors at the same scale.
Turbo VPN – The Tracker King
With 14 embedded trackers, Turbo VPN has the highest tracker count in the dataset. Its tracker list spans three separate national advertising ecosystems: Chinese platforms (Umeng, Mobvista, CloudMobi, DuApps), American platforms (Facebook's full suite, Google's ad stack, Flurry), and global ad mediation networks. It also connects to OFAC-flagged Chinese domains.
VPN 360 – Maximum Network Footprint
VPN 360 communicates with 105 unique hardcoded domains and contains 12 embedded trackers, including Mintegral (a Chinese ad platform), Facebook Ads, and multiple mediation platforms, including ironSource, Unity3D Ads, Fyber, and InMobi. It connects to OFAC-flagged baidu.com infrastructure.
Secure VPN – High Permissions, Heavy Tracking
Secure VPN requested 24 total permissions, tied for the highest in the dataset, with 5 dangerous permissions, including location tracking. It embedded 7 trackers, including the full Facebook tracking suite of Ads, Analytics, Login, and Share SDK. The combination of extensive location access and Facebook's behavioral profiling infrastructure in a single app is a notable concern.
Full App Comparison Table
The table below provides a comprehensive side-by-side comparison of all 18 VPN apps analyzed, with dark purple indicating high risk and light purple indicating moderate concern:
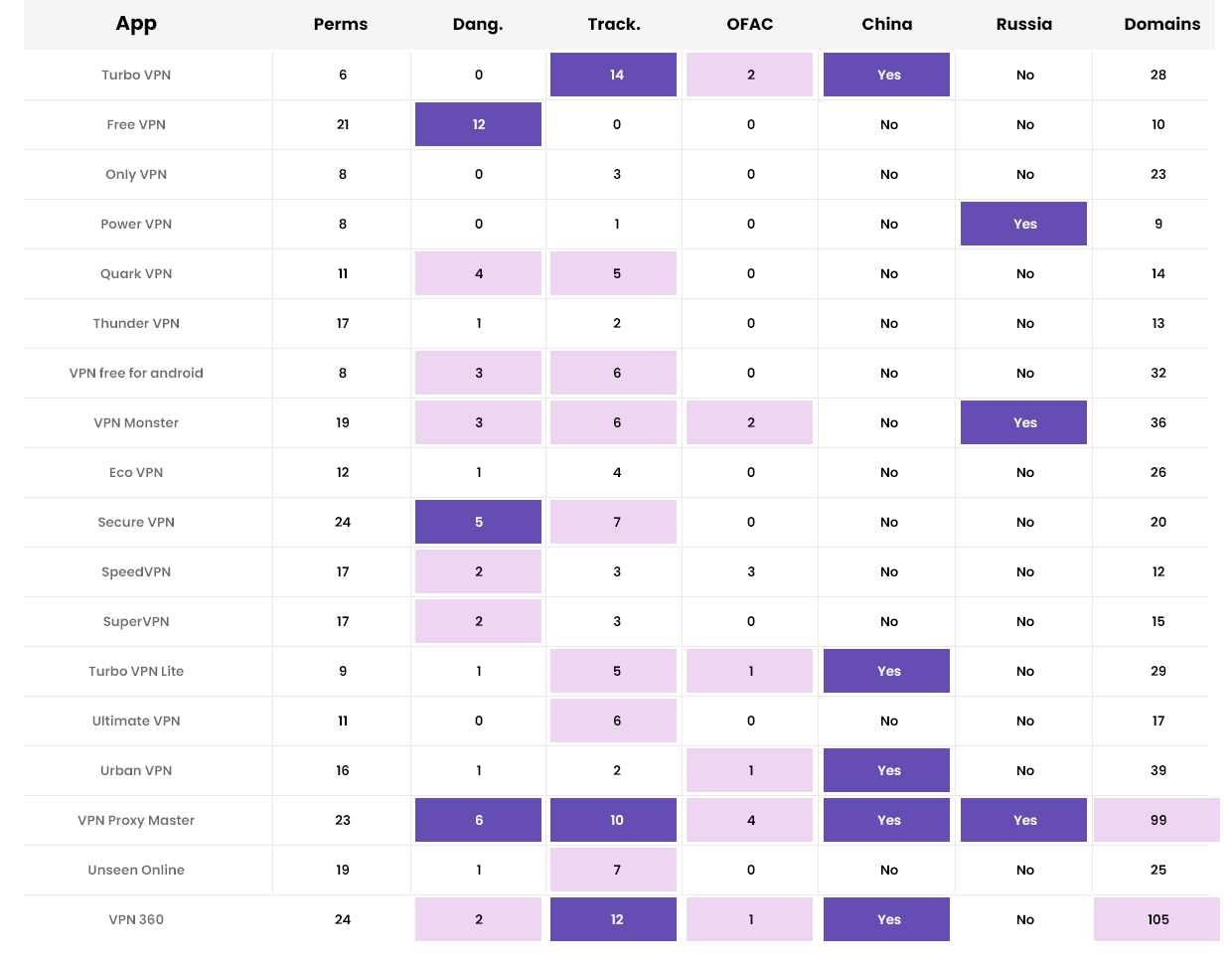
Disclaimer: Data was captured in March 2026.
What You Should Do Before Installing a Free VPN
The central finding of this research is straightforward: the overwhelming majority of popular free VPN apps on Android are not primarily privacy tools. They are data collection and advertising platforms that provide VPN functionality as a lure. The business model is clear, and the mechanisms for executing it are built into the app before a user ever opens it.
A few practical steps follow directly from the research:
- Check declared permissions before installing. A VPN app that requests access to your camera, microphone, contacts, or call logs is requesting access it does not need. Deny these permissions or do not install the app.
- Use Exodus Privacy to audit tracker counts. Before installing any app, search for it at reports.exodus-privacy.eu.org to see how many trackers and permissions it contains.
- Be skeptical of free VPN apps. Server infrastructure is expensive. If a VPN charges nothing, that cost is being recovered somewhere else, and this research documents exactly where. Privacy and security are worth investing in.
- Prefer open-source, independently audited VPN solutions. Apps with published codebases and third-party security audits provide a level of transparency that closed-source free apps structurally cannot offer.
- Consider decentralized VPN alternatives. Decentralized VPN networks eliminate the single-point-of-trust problem inherent in traditional VPN services, making it structurally impossible for any single operator to collect or monetize user data at scale.
Until app stores enforce meaningful privacy standards for tools that explicitly market themselves as privacy tools, the burden of verification sits entirely with the user. The word "free" in a VPN app's description belongs in your threat model, not your feature checklist. In many cases, you’re actually better off not using any VPN at all than picking a free tool that will sell you out to compensate.
But in reality, it’s even wiser to recognize that your digital privacy and security hold immense importance and value, which keep growing by the day. Investing in these things doesn’t cost a fortune, and the return you get is absolutely worth it.
Be part of the resistance, quietly.
Get Mysterium VPN

Dominykas is a technical writer with a mission to bring you information that will help you in keeping your digital privacy and security protected at all times. If there's knowledge that can help keep you safe online, Dominykas will be there to cover it.

.png)