Tor vs VPN: Which One Offers Better Online Privacy and Security?

In an age where internet freedom is what we all wish for, it’s no surprise that many people are seeking ways to keep both their internet connection and internet activity secure.
Two popular methods for doing so are Tor and VPNs. Both technologies offer distinct approaches to safeguarding your data, but each comes with its own set of advantages and drawbacks.
If you’re looking to protect your online identity, you may be wondering: Which one is better, Tor vs VPN?
In this article, we’ll dive deep into the world of Tor and VPNs, providing a detailed comparison of the two. We’ll look at how they work, their pros and cons, and which one is the best fit for your online privacy needs.
Spoiler alert: there’s no clear winner between Tor and VPNs —but understanding the key differences can help you decide which one will best protect your data.
What is Tor?
Tor, short for "The Onion Router," is a decentralized network that aims to provide users with greater online anonymity.
Basically, Tor helps mask your internet activity by bouncing your connection through multiple Tor servers (nodes) before it reaches its final destination.
Each hop along the way encrypts the data, peeling away a layer of encryption each time, much like peeling the layers of an onion. This multi-layer encryption helps obscure your original IP address and location, making it difficult for third parties to trace your online activity back to you.
Tor is free to use and maintained by a global network of volunteer servers, meaning it operates without any central authority.
When you use Tor, your data passes through a series of volunteer-run nodes located around the world, with each node only able to see part of your connection, not the entire picture. The result is a highly decentralized network where users’ activities are extremely difficult to trace.
Despite its impressive encryption and anonymity features, Tor does come with a few drawbacks. First, using Tor can slow down your internet speed significantly.
Because your data is routed through several different nodes, each time you access a website or service, it may take longer for the connection to be established. In addition, while Tor encrypts your traffic, it doesn’t guarantee that no one will be able to intercept it.
If someone manages to compromise one of the nodes, they could potentially monitor your traffic and see what you're doing.
How Does Tor Work?
The Tor network works by encrypting your internet traffic and sending it through a series of nodes, each owned by a different volunteer.
These nodes act as relays, with each node only able to decrypt one layer of encryption and know where the traffic came from or where it is going.
This ensures that no single node knows the full picture of your online activity.
- Entry node: The first node your traffic hits is the entry node, which knows your IP address but not your final destination.
- Middle node: The middle node only knows where the traffic came from (the entry node) and where it is going next (the exit node).
- Exit node: The final node that sends your traffic to its destination. The exit node decrypts the final layer of encryption, revealing the data, but it cannot see the original IP address that initiated the request.
The Tor browser is the tool you use to access the Tor network, ensuring that all the traffic passing through the network is properly routed and encrypted.
While Tor encrypts your internet traffic and makes it very difficult to track your activities, there are still risks, particularly at the exit node. If a malicious actor controls an exit node, they may be able to view your internet traffic.
Use Cases for Tor
Here are the most common reasons why people use the TOR browser.
Maximized Anonymity
Tor is widely used by those in high-risk environments to protect their identity and communicate safely without fear of government surveillance. It's particularly useful for those operating in countries with heavy censorship or oppressive regimes.
Bypassing Censorship
In countries with strict internet censorship (like China or Iran), Tor allows users to access restricted websites and communicate freely without the prying eyes of government entities.
Accessing the Dark Web
Tor is the primary method to access the dark web, a part of the internet not indexed by traditional search engines.
It provides access to a wide range of anonymous services, often for private transactions, communication, and forums.
Privacy for Research and Communication
Tor can be a tool for individuals who want to engage in private online research or communicate sensitive information without revealing their IP address or physical location.
Avoiding Tracking by Advertisers
Tor hides your identity from advertisers and websites that track you across sessions, which can be ideal for those who wish to maintain online anonymity and avoid targeted ads.
Secure Browsing for Sensitive Topics
For users concerned about their internet service provider (ISP) monitoring their activities, Tor offers a layer of security, making it difficult for third parties to see what sites they visit or what they do online.

What is a VPN?
A VPN, or virtual private network, works differently from Tor. Rather than bouncing your traffic through multiple nodes, a VPN creates a secure encrypted tunnel between your device and a VPN server.
This means that your data is routed through a remote server (which can be in another country) before it reaches its destination on the web.
A VPN essentially hides your true IP address, replacing it with the IP address of the VPN server you're connected to. This gives the impression that you are browsing from another location, making it much harder for third parties to track your real identity.
The VPN connection works by encrypting your data along the way, using encryption protocols like OpenVPN or WireGuard, which are robust and widely considered secure.
When you use a VPN, all of your internet traffic is encrypted, which prevents hackers, ISPs, and even governments from spying on your online activities.
Unlike Tor, which is a decentralized network of volunteer servers, a VPN relies on a centralized network of servers that are owned and maintained by the VPN provider.
This means that VPN providers often have access to your connection logs, and depending on their privacy policy, they may collect data on your online activity. However, many VPN providers offer a no-logs policy, ensuring that they don’t track your browsing behavior.
One major advantage of a VPN over Tor is speed. Since a VPN only routes your data through a single VPN server, you’ll likely experience faster speeds than with Tor, which can be sluggish due to the many nodes your traffic passes through.
For activities that require high bandwidth, such as streaming or online gaming, VPNs are typically the better option.
How Does a VPN Work?
A VPN works by creating an encrypted tunnel between your device and a VPN server. When you connect to a VPN, all of your internet traffic is rerouted through the VPN server, which is typically located in a different geographical region.
This masks your true IP address and gives you a new IP from the VPN server, making it appear as though you are browsing from a different location.
The data traveling through the VPN connection is encrypted using strong encryption protocols like AES-256, which ensures that even if someone intercepts the data, they won’t be able to read it.
This encryption protects your sensitive information from hackers, ISPs, or any third parties attempting to monitor your online behavior.
A VPN also secures your internet traffic from the moment it leaves your device until it reaches the VPN server, creating a protected encrypted tunnel.
Depending on the VPN provider you choose, you may be able to connect to VPN servers in various countries, giving you more flexibility to access content that may be geo-blocked in your region.
Use Cases for VPN
Let's take a look at the most common uses of a VPN.
Securing Public Wi-Fi Connections
When connected to public Wi-Fi, such as in cafes or airports, a VPN creates an encrypted tunnel to protect your data from hackers who might be lurking on the same network.
Bypassing Geo-Restrictions and Accessing Content
A VPN allows users to connect to servers in different countries, helping them bypass geo-blocks and access content from services like Netflix, Hulu, BBC iPlayer, or other region-restricted platforms.
Enhanced Online Security
A VPN is beneficial for ensuring your online transactions (shopping, banking, etc.) are secure. By encrypting your data, it prevents attackers from intercepting sensitive information like credit card numbers or passwords.
Privacy from Your ISP
Using a VPN stops your ISP from seeing your online activities. This can be useful for users who wish to keep their browsing history private or avoid bandwidth throttling based on usage patterns.
Remote Work Access
Many businesses use VPN services to give employees remote access to the company’s internal network. A VPN server can provide a secure connection to corporate resources while maintaining data privacy.
Avoiding Website Tracking and Ads
A VPN helps mask your IP address, which can reduce tracking by websites, advertising networks, and analytics services that use your online behavior to target you with ads.
Secure Communication
Individuals and companies who prioritize secure communication (whether for emails or instant messaging) use VPNs to encrypt their data, protecting sensitive conversations from being intercepted.
Gaming with Privacy
Gamers use VPN services to hide their IP address, reduce latency, and avoid DDoS attacks while gaming online. A VPN server can also help gamers access games or content restricted to specific regions.
What Is a Decentralised VPN (DVPN)?
A decentralized VPN mimics the architecture of Tor more closely but has the same ease of use as a VPN.
As a peer-to-peer system (P2P), people can earn by sharing their IPaddress and helping to maintain the network. VPN users plug into a global network of nodes run by people voluntarily.
Unlike the Tor network, all nodes are paid to provide the VPN service and keep the network powered and safe.
Mysterium VPN is a decentralized VPN. It allows people to select the connection from a list of available nodes from around the world. Traffic is encrypted and directed through everyday devices rather than data center servers.
Tor vs. VPN: Key Differences
Let's take a look at the major differences between a VPN and the Tor network.
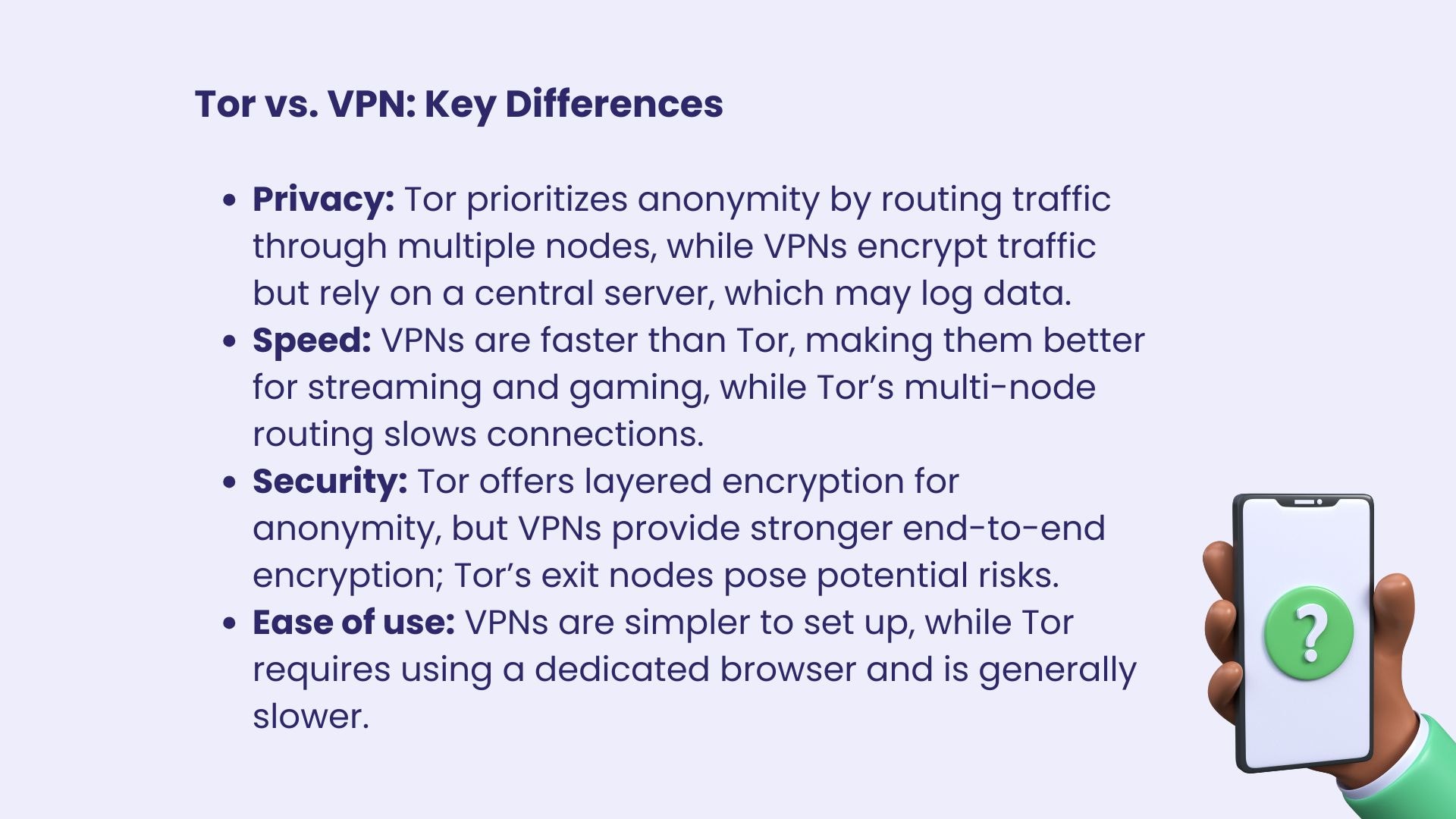
- Privacy: Tor is more focused on anonymity, ensuring that no single node can trace your entire traffic. A VPN, on the other hand, encrypts your traffic but routes it through a central server, meaning the VPN provider has access to your connection logs. This makes Tor more suitable for users who want the highest level of online privacy, while a VPN may be better for those who want both privacy and speed.
- Speed: VPNs are generally faster than Tor because they route traffic through one secure VPN server rather than multiple nodes. This makes VPNs more suitable for activities like streaming, gaming, and other data-intensive tasks, whereas Tor can be slow due to the multiple nodes your traffic has to pass through.
- Security: Both Tor and VPNs encrypt your internet traffic, but Tor provides more anonymity because it uses multiple layers of encryption and routes your data through several volunteer-run nodes. However, VPNs typically offer more robust encryption protocols and can protect your data from end to end. The risk with Tor lies in the exit node, where the traffic is decrypted and could potentially be monitored or altered.
- Ease of use: VPNs are easier to set up and use for most people. Once you subscribe to a VPN provider and install the software, you're good to go. On the other hand, using Tor requires downloading and using the Tor browser, which is a bit more involved and can be slower.
Can You Use Tor and VPN Together?
Yes, it’s possible to use VPN and Tor together for an added layer of privacy and security. By first connecting to a VPN and then using the Tor browser, you encrypt your traffic twice—once with the VPN’s encryption and again with Tor’s multi-layer encryption.
This approach can give you the benefits of both worlds: the anonymity of Tor and the VPN’s encrypted tunnel, ensuring that even if a malicious exit node intercepts your traffic, they won't know your true IP address.
However, using both can cause a significant slowdown in your internet speed, so it’s not ideal for high-bandwidth activities.
Alternatives to the Tor Network
While Tor is one of the most popular tools for maintaining online anonymity, there are several other options that can offer similar privacy features, each with its own strengths and weaknesses.
The Invisible Internet Project (I2P) is a decentralized alternative to Tor, focusing on anonymous browsing and file sharing. It encrypts and routes traffic through a series of volunteer-run routers and is specifically designed for hidden services.
Although its speeds are slower than Tor’s, it’s a solid choice for users seeking privacy in a decentralized network, but it’s not as widely used as Tor.
For those looking for more advanced privacy setups, Whonix and Tails are operating systems that route all traffic through Tor. Whonix is designed for users who want to ensure that all their activities are anonymized, while Tails runs from a USB stick, leaving no trace after use.
These solutions provide an additional layer of security but can be more complex to set up and use.
Lastly, Freenet and Zeronet offer decentralized, censorship-resistant browsing, with Freenet focusing on file-sharing and anonymous communication and Zeronet allowing for the creation of decentralized websites.
While they both offer anonymity, they’re not as mainstream and can be slower than more traditional methods like VPNs.
Conclusion
Whether you choose Tor or a VPN, your online privacy is too important to ignore.
Tor provides exceptional anonymity but can be slow and risky at times, especially when using compromised exit nodes. VPNs, on the other hand, offer faster speeds and more reliable connections, with a secure encrypted tunnel protecting your traffic.
By understanding the differences between Tor vs. VPN, you can choose the best option for your privacy needs—whether you want a secure VPN server or the added layers of Tor encryption.
Protect Yourself Online. Try Mysterium VPN Risk-Free.
Get Mysterium VPN
Frequently Asked Questions

Gintarė is a cybersecurity writer at Mysterium VPN, where she explores online privacy, VPN technology, and the latest digital threats. With hands-on experience researching and writing about data protection and digital freedom, Gintarė makes complex security topics accessible and actionable.

.png)