EU Members Sold Spyware to Rights Abusers While Brussels Rewrote the Rules

Key Takeaways
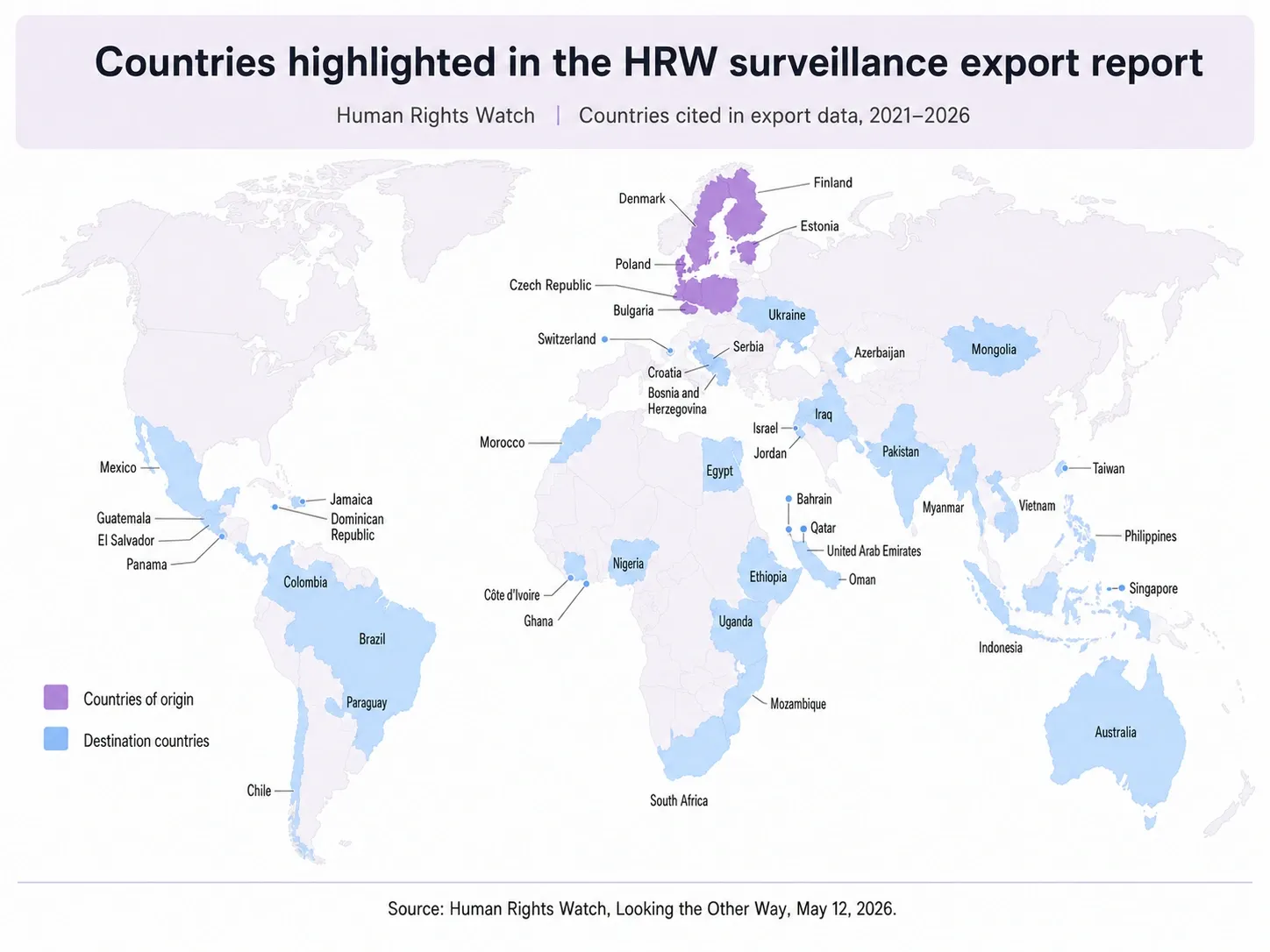
- Human Rights Watch found six EU member states (Bulgaria, Czech Republic, Denmark, Estonia, Finland, and Poland) exported surveillance technology to over 40 countries, including Azerbaijan, Rwanda, Myanmar, Ethiopia, Egypt, UAE, and Bahrain, all with documented records of using such tools against journalists, activists, and dissidents.
- The EU's 2021 Dual-Use Regulation requires member states to consider the human rights record of recipient countries before granting export licenses, but the word "consider" carries no enforcement teeth.
- The Commission's January 2024 implementing guidelines gut transparency by separating technology data from destination data into distinct spreadsheets, making it impossible to link which technology went where.
- Twelve of 27 EU member state export authorities denied or ignored freedom of information requests, with Europe's largest surveillance exporters (France, Germany, Italy, and Spain) denying all access.
- The EU Commission is due to begin evaluating the Dual-Use Regulation in September 2026, the precise window HRW is targeting with this report.
The Law That Said "Consider" When It Should Have Said "Stop"
Poland's Ministry of Economic Development and Technology reviewed Rwanda's human rights record before issuing a 2023 export license for telecommunications interception systems and concluded, in writing, that no risk was identified. Rwanda has been documented using Pegasus spyware against journalists and political dissidents since at least 2017, with authorities deploying extrajudicial killings, enforced disappearances, and systematic digital surveillance against critics at home and in the diaspora. No risk identified.
The Recast's human rights clause requires exporting countries to "consider" the rights record of the recipient country, not to refuse on that basis. Poland exercised that discretion, looked directly at the evidence, and decided it was fine. Bulgaria exported intrusion software and telecommunications interception systems to Azerbaijan between 2020 and 2023, despite security researchers finding substantial evidence that Azerbaijani authorities used Pegasus spyware to hack Armenian journalists and civil society during the 2023 conflict over Nagorno-Karabakh.
HRW found the same pattern across six EU member states in total. Bulgaria, Czech Republic, Denmark, Estonia, Finland, and Poland all exported cybersurveillance technology between 2021 and 2026, with recipient countries spanning four continents, many of which rank among the most documented abusers of surveillance technology against their own populations in the world.
The Recast also includes a "catch-all" clause requiring authorization for non-listed surveillance technology that could be used for internal repression, but it puts the burden on exporters to self-report risk, which is not in any commercial interest to do. It's a self-policing mechanism for an industry with every financial incentive to look the other way, not unlike how the EU funds governments that beat their journalists while insisting the rules are being followed.
How Brussels Rewrote Its Own Transparency Rules into Uselessness
The 2021 Recast required annual public reporting connecting exporting member state, type of technology, and destination country. MEP Markéta Gregorová, the Parliament rapporteur, said in 2021 that civil society would use this data to catch misuse. The Commission's January 2024 guidelines reinterpreted "by types of items and by destinations" to mean these are reported separately, in different spreadsheets, making it impossible to link a specific technology to a specific recipient country. The justification was exporter confidentiality, even though the Recast explicitly requires this data to be public.
HRW had to file freedom of information requests to all 27 EU member states to reconstruct what the Commission's annual reports were supposed to contain. Seven states provided data, twelve denied or ignored the requests, and the Commission itself refused its own request, citing confidentiality and encrypted transmission channels, with none of these justifications grounded in the Recast's actual text.
Sweden reported zero cybersurveillance applications, yet third-party trade data shows Swedish firm MSAB exporting forensic extraction devices to India every year since 2023, with those devices escaping controlled categories because they aren't "specially designed" for covert surveillance, a loophole the Commission's own guidelines acknowledge without closing.
September 2026 Is When the Excuses Run Out
The Commission begins evaluating the Dual-Use Recast in September 2026, and HRW has timed this report directly at that window. The ask is specific: require genuine due diligence rather than self-reporting, link technology to destination in annual reports, and establish that this data is public and not subject to commercial secrecy exemptions, the Recast's own text doesn't support.
For journalists, activists, and anyone else wanting to protect themselves in countries where EU-exported surveillance tech is already deployed, getting Mysterium VPN (with 82% off now) sure is a solution. But it's absurd that a substitute for a regulatory framework that's supposed to do the job is needed in the first place.
So now, the question for September 2026 is whether the same institution that rewrote its transparency rules to protect exporters in 2024 will decide that the people getting surveilled with EU-built technology matter more. Things need to change. And yet, I don't think the answer so far gives anyone reason for confidence.
Be part of the resistance, quietly.
Get Mysterium VPN

Dominykas is a technical writer with a mission to bring you information that will help you in keeping your digital privacy and security protected at all times. If there's knowledge that can help keep you safe online, Dominykas will be there to cover it.

.png)