Censorship is Control. Connection is Resistance
- Fight monitoring with 7,500+ residential IPs in 100+ countries.
- Protect your online activity with robust end-to-end encryption.
- Stay anonymous with IP masking and a built-in kill switch.

Justifying Digital Control Measures

Restrictions are rarely introduced as “censorship.” They’re framed as protection and concern for your well-being. But intention and impact aren’t always the same. Below are common reasons for internet regulations, their justifications, and what they actually mean for you in practice.
Protecting Kids ➡️ Age Verification ➡️ Mass Data Collection
Governments worldwide are passing age verification laws and banning kids from social media. This means uploading government-issued ID, submitting biometric data, or verifying your identity through third-party services. Just like that, a measure introduced to protect vulnerable minors can become an infrastructure that tracks everyone.
National Security ➡️ Expand Monitoring ➡️ Loss of Privacy
Security laws often expand intelligence agencies' ability to exercise surveillance on their people. This can include metadata collection from your browsing activities, ISP data retention mandates, and expanded cross-border intelligence sharing, with groups like Five Eyes. Surveillance systems built for exceptional threats can become permanent fixtures.
Fighting Misinformation ➡️ Platform Liability ➡️ Over-Moderation
Governments impose penalties on platforms that fail to remove harmful or illegal content quickly. So, to avoid fines, platforms frequently err on the side of “better safe than sorry” and sometimes end up suppressing lawful speech, controversial opinions, or independent journalism. Moderation becomes risk management.
Maintaining Order ➡️ Temporary Shutdowns ➡️ Normalized Disruption
Governments worldwide, including those in Iran and India, justify internet shutdowns during elections or protests to prevent unrest. Over time, “temporary” internet shutdowns have become a standard response tool, disrupting communication, journalism, and commerce. Connectivity becomes conditional.
Internet Restrictions Around the World
Internet restrictions don’t look the same everywhere. In some countries, entire online platforms and websites are blocked. In others, online restrictions sneak in through regulation, licensing laws, surveillance mandates, or good intentions.
The methods and reasons for control may be different. The result is the same – the internet isn’t free everywhere.
United States
In the United States, internet control manifests in several ways. Federal intelligence programs have historically enabled broad data collection capabilities. Internet service providers can see your browsing activity unless it’s encrypted, and data brokers are running wild. Certain states restrict online gambling access and age-restricted content in an attempt to protect children.
Social media platforms are experiencing mountains of ongoing political pressure regarding content moderation practices, including banning the platforms for young, vulnerable children, as well as accusations of shadowbanning and algorithmic suppression when discussing controversial topics, including politicians, their actions, and their potential shortcomings.
China
China operates a sophisticated internet filtering system, known as the “Great Firewall.” Major global platforms like Google, YouTube, Facebook, Instagram, and many international news outlets are blocked in the country. Traffic is monitored through deep packet inspection (DPI), and real-name registration laws link online activity to verified identities.
Content deemed politically sensitive is filtered, and domestic platforms operate under strict compliance requirements. The internet is built to be restricted, and people’s activity is monitored heavily.
Russia
Russia has consistently tightened control over how its citizens use the internet, especially when the country’s experiencing geopolitical tensions and domestic unrest. Independent media outlets are blocked or forced to shut down, while Western social platforms are restricted or banned. The government has expanded its “sovereign internet” framework.
This is infrastructure built to isolate the Russian part of the internet from the global web if necessary. Increased monitoring and content controls have followed, with laws punishing what authorities classify as “false information.” People do have access to the internet, but the government is closely watching you.
Iran
Iran often restricts people’s access to global social media platforms and messaging apps. During protests and periods of civil unrest, nationwide internet shutdowns are implemented to limit coordination and information sharing. Strict filtering systems and monitoring are used to regulate Iranian’s access to news, political content, and communication tools.
Access can change rapidly depending on political conditions. The people of Iran have access to the internet, but that connection is incredibly fragile and conditional on the whims of local politicians.
Europe
Across Europe, internet access remains largely open, but regulatory control is tightening. The EU has introduced sweeping digital legislation, including the Digital Services Act (DSA) and the Digital Markets Act (DMA), imposing significant compliance obligations on large online platforms operating in member states. These laws increase platform liability for illegal content and misinformation, encouraging faster removals and stricter moderation systems.
The United Kingdom & France
Overall, people in the UK and France, like the rest of Europe, can enjoy relatively free internet access. However, both countries are currently trying to pass laws that would ban children under 16 from using social networking sites.
To prove you’re older than 16, UK and France residents would need to verify their age (and, in turn, their identity), which means everyone, including legal adults, would have to hand over their government-issued IDs if the social media platform they’re using suspected that they’re younger than 16. People in Europe have the privilege of a reasonably free internet connection, but that doesn’t mean they should take it for granted.
From total firewalls to regulatory tightening, the pattern is clear: government oversight is expanding, restrictions are evolving, and access is becoming increasingly conditional. Control rarely appears overnight. It scales gradually, so that you won’t notice until it’s too late.
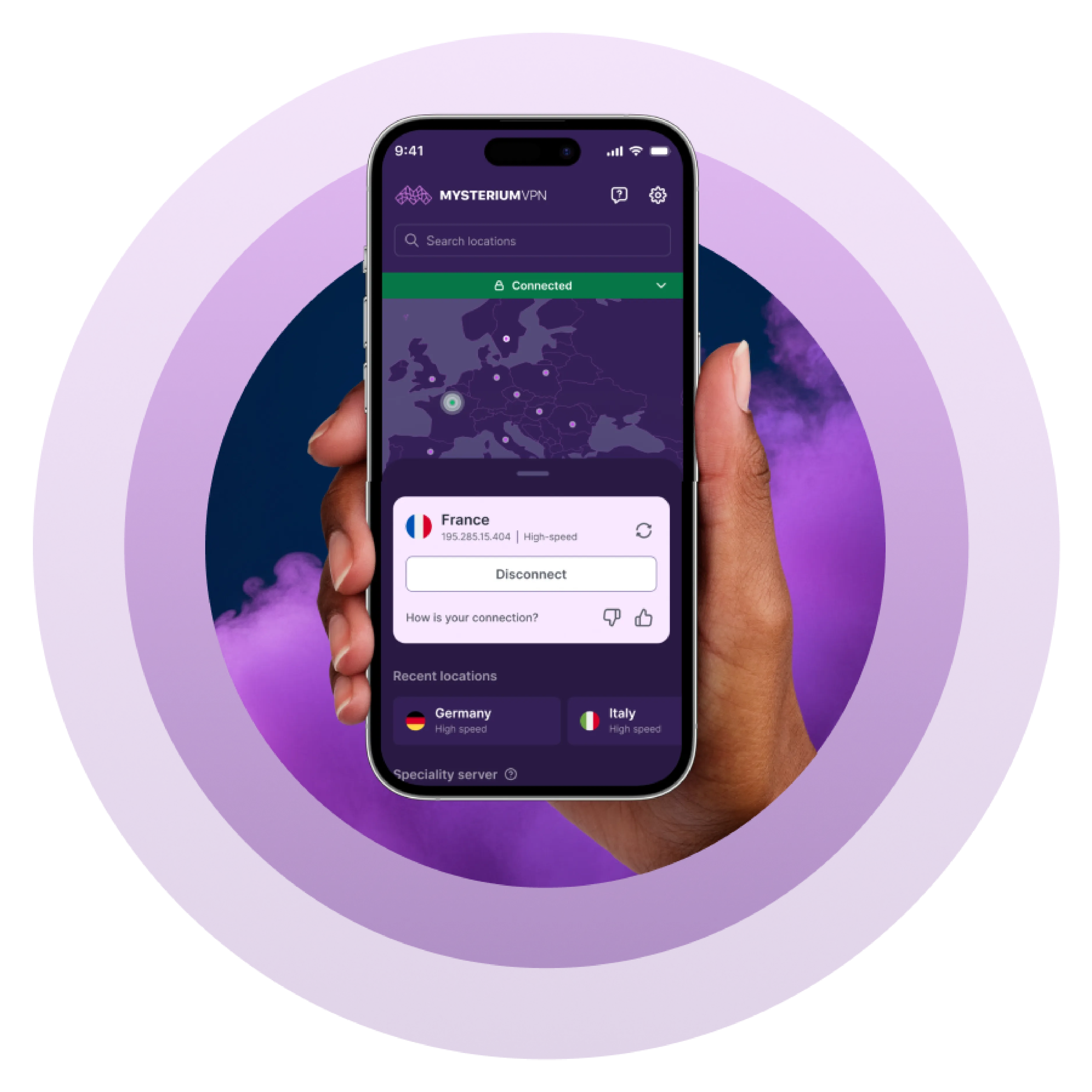
How Mysterium VPN Protects Digital Autonomy

As monitoring expands and restrictions evolve, privacy tools become a must-have for everyone who cares about their privacy. A VPN doesn’t change laws. It changes your exposure to them.
Enjoy Global Content
Many internet restrictions are enforced through IP-based filtering or DNS-level blocking. When your location determines what you can access, geography becomes a gatekeeper.
A VPN routes your connection through a different exit point, making your traffic appear to originate from another region. This can restore access to services or websites that are limited or blocked locally.
It doesn’t remove regulation, but it reduces the effectiveness of location-based controls. In environments where access depends on your location, rerouting your connection changes the equation.
Encrypt Your Internet Activity
Without encryption, your internet service provider (ISP) can see the domains you connect to and the timing of those connections. In some jurisdictions, ISPs are even required to retain metadata for defined periods or provide it upon request.
A VPN creates an encrypted tunnel between your device and the VPN network. While connected, your ISP can see that you’re using a VPN, but not the specific sites or services you access through it.
Encryption doesn’t make activity invisible to all parties. Instead, it limits routine visibility at the access-provider level, where much passive monitoring occurs. Reducing default exposure strengthens baseline privacy.
Reduce Tracking and Profiling
IP addresses are frequently used to estimate your approximate location, identify users across sessions, and support behavioral profiling. When your IP address remains static, it becomes an anchor point for correlation across websites, services, and data brokers.
A VPN replaces your publicly visible IP address with one from its network, making it harder to directly associate browsing activity with a single household or physical connection.
This doesn’t eliminate tracking entirely, as browser fingerprinting and account-based tracking still exist, but it reduces one of the most common and persistent identifiers used online.
Add Protection on Public Wi-Fi
Public Wi-Fi networks are inherently shared, unsafe environments. In unsecured or poorly configured networks, traffic interception or man-in-the-middle (MITM) attacks can happen.
Using a VPN encrypts traffic before it leaves your device, reducing the risk of local interception on open networks such as airports, hotels, cafés, or co-working spaces. Even when websites use HTTPS, VPNs add an encryption layer across all applications and services on your device.
In a world of expanding online monitoring and filtering, VPNs are a practical, low-effort tool to keep the internet closer to what it was designed to be: open and accessible to everyone.
The Future of the Internet Is a Choice
The internet is changing. In some countries, it’s openly controlled. In others, it’s gradually regulated, filtered, and monitored in the name of people’s protection, safety, or security.
The direction isn’t inevitable. An open internet that we’ve known and loved depends on resilient infrastructure, and on people choosing tools that protect their autonomy, free access, and online privacy. It’s up to you to fight back and take back the internet. Join us today!